Privacy advocates are growing leery of the Tor network these days, as recently published research has shown a great number of network’s exit relays are compromised. Furthermore, on September 15, the Hacker Factor Blog published a new Tor report that shows IP addresses being uncovered. The paper called “Tor 0-day” says that it is an open secret among the internet service community: “You are not anonymous on Tor.”
For years now, a great number of digital currency proponents have utilized Tor and virtual private networks (VPNs) to stay anonymous while sending bitcoin transactions. The Tor Project was released 17 years ago in 2002, and it has always claimed to obfuscate internet traffic for the end-user.
Essentially, the software written in C and Python leverages a volunteer overlay network consisting of thousands of different relayers. The very basics of this network are meant to conceal a user’s activity on the internet and allow for unmonitored confidential communications.
However, since Covid-19 started and during the months that followed a number of individuals have exposed a few of Tor’s weaknesses. One Tor vulnerability exposed in August is the large-scale use of malicious relays.
A paper written by the researcher dubbed “Nusenu” says 23% of Tor’s current exit capacity is currently compromised. Nusenu also warned of this issue months ago in December 2019 and his research fell on deaf ears. Following Nusenu’s critique, another scathing report called “Tor 0-day” details that IP addresses can be detected when they connect directly to Tor or leverage a bridge.
The paper “Tor 0day” stresses that it is pretty much an “open secret” between those who know, that users “are not anonymous on Tor.” The research is part one of a new series and a follow up will publish data that describes “a lot of vulnerabilities for Tor.” The hacker describes in part one how to “detect people as they connect to the Tor network (both directly and through bridges)” and why the attacks are defined as “zero-day attacks.”
Further, the blog post shows the reader how to identify the real network address of Tor users by tracking Tor bridge users and uncovering all the bridges. The study shows that anyone leveraging the Tor network should be very leery of these types of zero-day attacks and what’s worse is “none of the exploits in [the] blog entry are new or novel,” the researcher stressed. The Hacker Factor Blog author cites a paper from 2012 that identifies an “approach for deanonymizing hidden services” with similar Tor exploits mentioned.
“These exploits represent a fundamental flaw in the current Tor architecture,” part one of the series notes. “People often think that Tor provides network anonymity for users and hidden services. However, Tor really only provides superficial anonymity. Tor does not protect against end-to-end correlation, and owning one guard is enough to provide that correlation for popular hidden services.”
Moreover, the blog post says that the next article in the series will be a brutal critique of the entire Tor network. It doesn’t take too much imagination to understand that in 17 years, entities with an incentive (governments and law enforcement) have likely figured out how to deanonymize Tor users.
“Someone with enough incentive can block Tor connections, uniquely track bridge users, map exit traffic to users, or find hidden service network addresses,” the first “Tor 0-day” paper concludes. “While most of these exploits require special access (e.g., owning some Tor nodes or having service-level access from a major network provider), they are all in the realm of feasible and are all currently being exploited.”
The paper adds:
That’s a lot of vulnerabilities for Tor. So what’s left to exploit? How about… the entire Tor network. That will be the next blog entry.
Meanwhile, there is another privacy project in the works called Nym, which aims to offer anonymity online but also claims it will be better than Tor, VPNs, and I2P (Invisible Internet Project).
Nym’s website also says that Tor’s anonymity features can be compromised by entities capable of “monitoring the entire network’s ‘entry’ and ‘exit’ nodes.” In contrast, the Nym project’s ‘lite paper’ details that the Nym network “is a decentralized and tokenized infrastructure providing holistic privacy from the network layer to the application layer.”
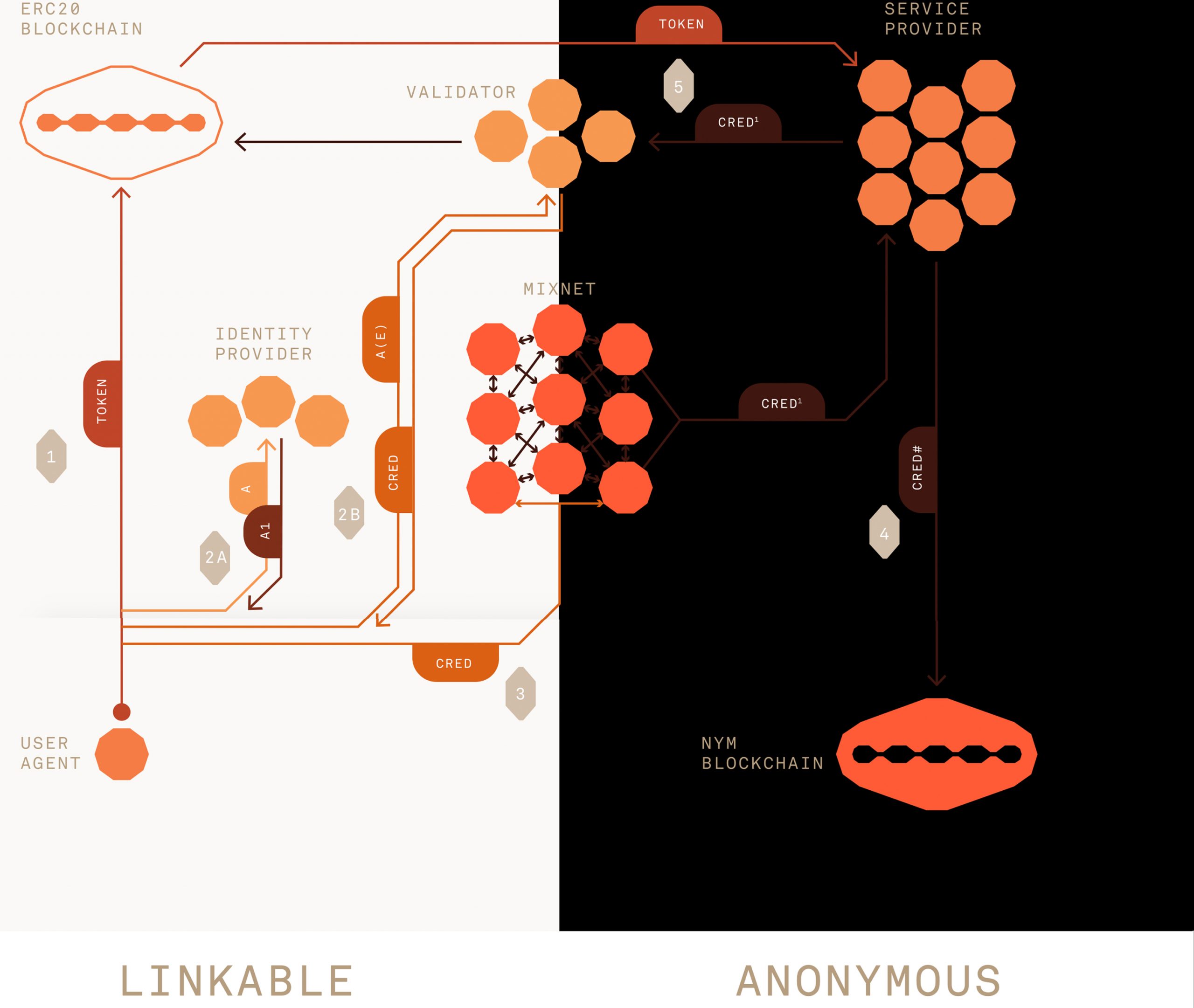
Nym utilizes a mixnet that aims to protect a user’s network traffic and mixes are rewarded for the mixing process.
“The intensive but useful computation needed to route packets on behalf of other users in a privacy-enhanced manner—rather than mining,” the lite paper explains. Furthermore, Nym is compatible with any blockchain as the “Nym blockchain maintains the state of credentials and the operations of the mixnet.”
The Nym team recently invoked a tokenized testnet experiment and is leveraging bitcoin (BTC) for rewards. The announcement says that a great number of people set up mixnodes and they had to close the testing round because it had gone over 100 mixnodes. Although, individuals can set up a mixnode to be prepared for the next round, the Nym development team’s website details.
What do you think about the Hacker Factor Blog’s scathing review concerning Tor exploits? Let us know what you think about this subject in the comments section below.
The post ‘You Are Not Anonymous on Tor’ – Study Shows Privacy Network Offers Superficial Anonymity appeared first on Bitcoin News.