Hardware wallet manufacturer Ledger, which sold over one million devices last year, has alerted its users to a major attack vector that’s recently been discovered. Although there are no reported cases of the attack being successfully deployed, the threat itself is very real. Today, Ledger urged users of its cryptocurrency wallets to take steps to avoid falling prey to the address spoofing attack.
Also read: Dead again? In Reality Bitcoin Is Up 729% Since Last February
Beware the Man in the Middle
Hardware wallets are regarded as one of the safest means of storing bitcoin and other cryptocurrencies. The USB cold storage devices eliminate the sort of attack vectors synonymous with being connected to the web. But to send funds or issue a receiving address, a hardware wallet has to be plugged in to an internet-enabled device, and researchers have discovered a vulnerability that affects Ledger devices at this stage. A newly published report reveals the way the MiTM attack would play out. It explains:
Ledger wallets generate the displayed receive address using JavaScript code running on the host machine…malware can simply replace the code responsible for generating the receive address with its own address, causing all future deposits to be sent to the attacker.
The attack, if executed, would leave the victim unaware at first that anything was the matter. To prove the the vulnerability is real, the report’s authors have posted a proof of concept that demonstrates the attack in action. The severity of the attack is heightened by the fact that, with Ledger’s wallet software stored in the AppData folder, it is relatively easy for malware to modify the receiving address. As the report notes, “All the malware needs to do is replace one line of code…this can be achieved with less than 10 lines of python”.

A Solution of Sorts
To avoid succumbing to this attack, there is a means of verifying the receiving address is correct, as the report explains, and as Ledger acknowledged in a tweet earlier today:
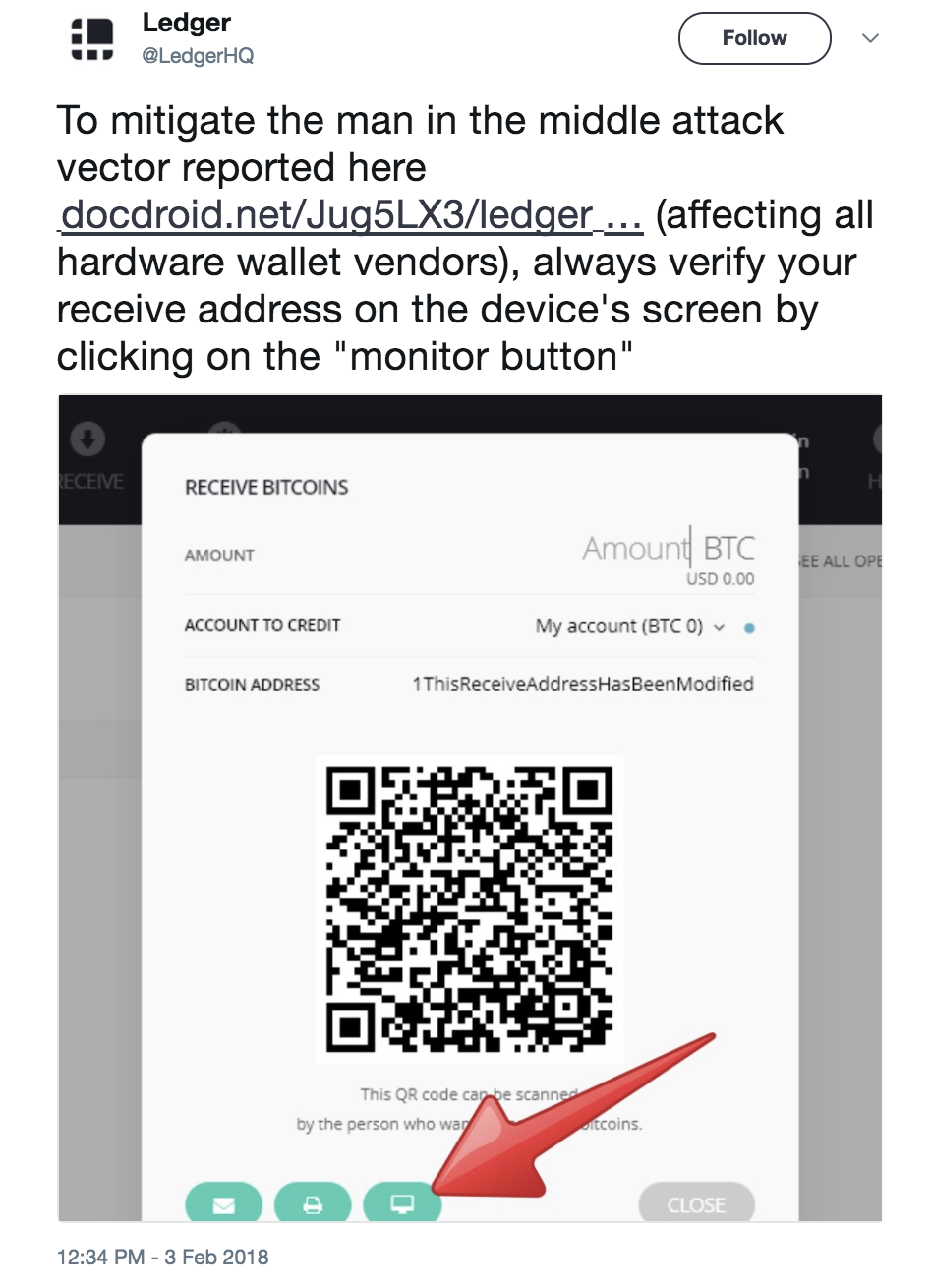
This solution, while effective, is not failsafe in that it’s reliant on the user remembering to follow this procedure every time they transact. As the report points out, “A proper solution would be to [force] the user to validate the receive address before every receive transaction, just like the wallet [forces] the user to approve every send transaction”.
That’s the system that Trezor now uses with its hardware wallets, mandating the use of 2FA simply to access the receiving address. It is hoped that Ledger will follow suit in updating its devices to adopt this methodology. Hardware wallets are still significantly safer than leaving funds stored on a centralized exchange, but no solution is entirely foolproof, as the Ledger case demonstrates.
Do you think this vulnerability is cause for concern and do you think Ledger should enforce 2FA to resolve it? Let us know in the comments section below.
Images courtesy of Shutterstock, and Ledger.
Need to calculate your bitcoin holdings? Check our tools section.
The post Ledger Addresses Man in the Middle Attack That Threatens Millions of Hardware Wallets appeared first on Bitcoin News.